Microsoft Teams Shared Channels feature was released to Public Preview just a few weeks ago. By default, external collaboration on shared channels is disabled with Azure AD Cross-tenant access policies. Collaboration in shared channels between organizations relies on the Azure AD B2B direct connect feature, which allows organizations to set up a mutual trust relationship. Users can work in shared channels with their home tenant accounts, there is no need to invite users as guests and switch between tenants.
Want to know how shared channels work, read my earlier blog post: https://mattipaukkonen.com/2022/04/28/introduction-to-microsoft-teams-shared-channels/
Cross-tenant access policy
Cross-tenant access settings are found underneath External Identities blade on Azure AD.
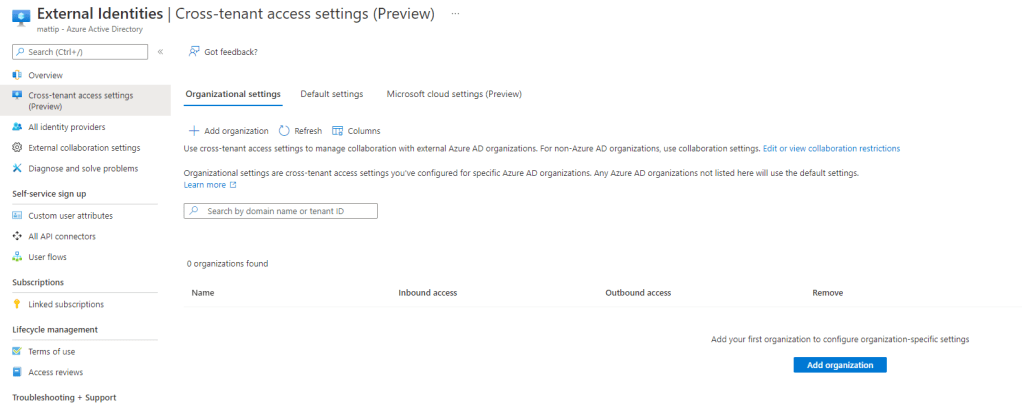
Regarding shared channels and B2B direct connect, settings are divided in two sections
- Organizational settings: allows to setup B2B direct connect with specific organization (also allows to block organizations)
- Default settings: controls to allow or block access with all Microsoft 365 tenants
Settings are divided into Inbound access settings, which controls access from other organizations to your tenant, and Outbound access settings, which controls access of your tenant users to collaborate with other organization.
Setting up mutual trust between organizations with B2B direct connect
Of course, first, you need to agree on how are you collaborating together, who is creating shared channels, is it a two-way collaboration, and who is the owner of the data.
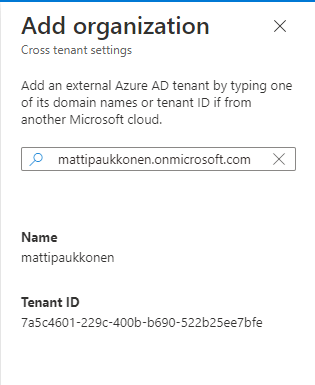
Open the Organization settings tab and click Add organization. Enter the partner organization’s tenant ID or domain name, and click Add from the bottom.
Now you can control Inbound and outbound access with that specific organization.
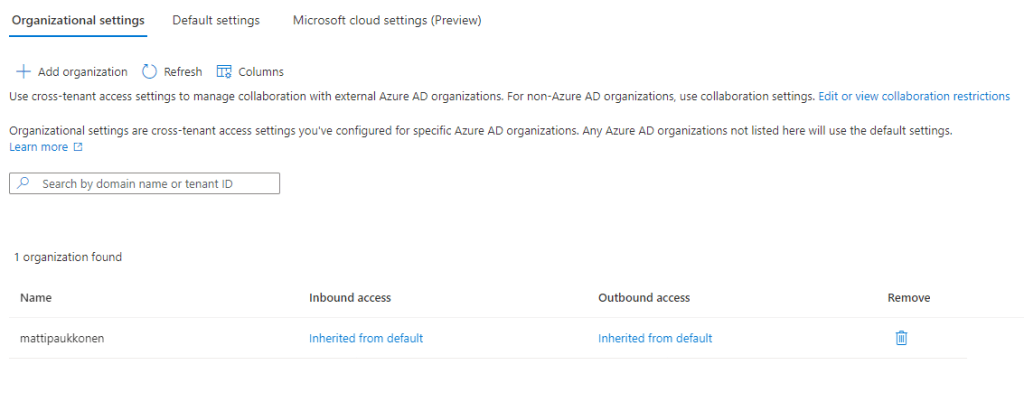
Now, let’s set up inbound access for that organization, so their users can access my tenant’s shared channels. Click Inbound access settings.
Open B2B direct connect tab and select Customize settings.

Select Allow access for both External users and groups and Applications tabs, both are needed. Applies to settings now enable access for all users and groups from the partner tenant.
Inbound access is now configured with the partner organization.
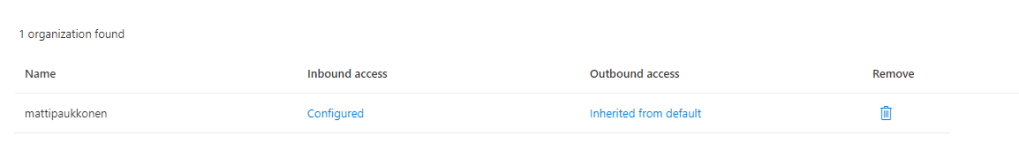
This configuration means that your organization is creating needed shared channels. The partner organization needs to enable outbound access with your organization in their tenant’s cross-tenant access policy.
How about sharing a channel with more than two organizations
First, agree on which organization is the owner of the shared channel. The owner organization is setting up inbound access for other organizations, creating the channel, and inviting members from other organizations. Other organizations are setting up outbound access with the owner organization, they don’t need to set up trusts between them.
Summary
Starting collaboration between two or more organizations always requires a common agreement on how we are working together. With shared channels, there is also a technical requirement for the IT department to set up. My suggestion is to start with a more controlled way and set up trusts directly with organizations. In the future settings can be opened up, just by allowing inbound and outbound access on default access settings.
Discover more from Enabling the Future of Work with Matti
Subscribe to get the latest posts sent to your email.